Our Services

Our Company
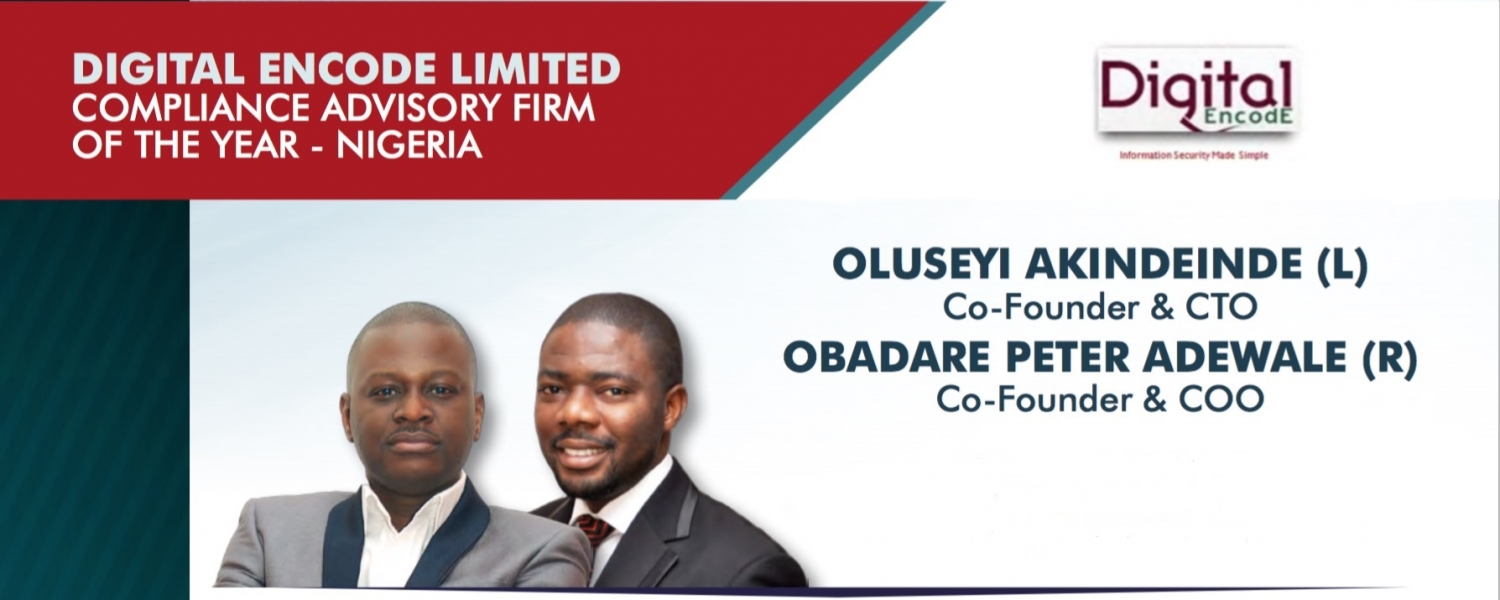
Digital Encode is a leading consulting and integration firm founded in 2003 that specializes in the design, management, and security of business-critical networks, telecommunications environments and other Information Technology (IT) infrastructures.
Recognized in the industry for its vendor independent perspective, the firm’s expertise lies in solving multifaceted, complex enterprise network security and audit problems.. View More